Portable Passcape Windows Password Recovery Advanced v15.2.1.1399
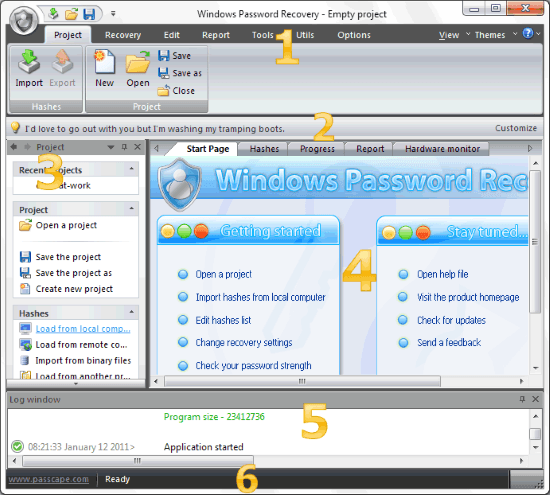
Welcome to Windows Password Recovery Portable, a network security analyzer, and Windows password recovery utility. Windows Password Recovery Portable tool is the only solution that implements the most advanced, patented password recovery technologies developed in Passcape Software, such as Artificial Intelligence or Pass-phrase attack. Compared to similar products, Windows Password Recovery Portable features a number of competitive advantages:
For home users – easy setup and use. Easily recovers or resets forgotten passwords to any Windows account.
For system administrators – password audit reveals security breaches, helping the administrators to ensure the reliability and security of the corporate network. Checks the security level of Windows operating systems.
For forensics, industry, and government security experts – analyzes and audits system security policies, issues recommendations on improving the stability of the operating systems’ password protection.
Features:
- Contemporary, easy customizable graphical user interface.
- Imports hashes from 10 other programs.
- Imports LM, NTLM, and DCC hashes directly from SAM, SECURITY, or NTDS.DIT; even if the files are locked by the system, the program still reads them.
- Imports hashes from remote computers.
- Imports hashes from system shadow copies, restore points, backups, and repair folders.
- Full support for Windows PIN.
- Support for cloud cached account, both Microsoft and Azure AD.
- Extracts BitLocker recovery passwords.
- Backs up local registry and Active Directory database.
- Imports password history hashes.
- Recovers some account passwords instantly. A mimikatz-like passwords extraction from memory. Cleartext password decryption from Windows Cache, Windows Hello, hidden secrets, and so on.
- Supports Active Directory (domain accounts).
- Supports importing from 64-bit systems.
- Exports hashes to the PWDUMP file.
- The software has 18 types of different attacks. 10 of them are unique, implemented upon patented technologies, and used in our products only.
- The program supports multithreading, fully leveraging the power of modern computers.
- Dictionary attack supports text dictionaries in the ASCII, UNICODE, UTF8, PCD, RAR, and ZIP formats.
- Broad choice of online dictionaries for dictionary attacks (about 2 GB). Not enough? Look at our ultimate and unique 30 GB wordlist collection.
- Some of the program’s functions – e.g., word mutation – are unique. For example, the total number of mutation rules exceeds a hundred and fifty. Not any other similar application features that!
- Supports an unlimited number of hashes.
- Supports for long (up to 255 characters) passwords.
- Artificial Intelligent analysis of found passwords.
- High search speed on modern computers – billions of passwords per second using GPU power.
- Includes auxiliary tools: hash generator, password strength check, rainbow table generators, SAM/SECURITY/NTDS.DIT backup tool, asterisk password revealer, resetting user password directly in the registry or Active Directory files, SAM, and NTDS.DIT explorers, DPAPI offline decoder, Windows Hello offline decoder, searching passwords by indexing disk sectors, etc.
- Useful wordlist utilities
- Advanced password reports
- Event notifications
- And much more…
Requirements:
1 GB RAM, OS based on Windows® NT (Windows XP/2k3/2K8/Vista/7/8/10/11/2012/2016/2019/2021), 100 Mb HDD space.
To run a GPU-based attack, you will need a CUDA-based video card with compute capability 3.0, AMD Radeon 7xxx+ GPUs, and Intel HD Graphics 4xxx and higher.
Compatibility:
For recovering hashes using NVidia GPU, you will need Windows XP or higher OS. AMD Radeon cards require Windows Vista or higher OSes.
Supported languages:
English, Chinese, French, Italian, Russian, Spanish. Add yours and get free registration.
Limitations:
Some of the program’s features (eg. dumping hashes from Volume Shadow Copies) are required Administrator privileges.
Release Notes:
[+] Support for some new GPUs.
[*] Update for Brazilian language interface.
[!] Several issues decrypting TPM-protected data have been fixed.
This version now allows decrypting data encrypted with TPM
(for example, DPAPI blobs or Windows Hello passwords) on the
original and properly loaded PC or laptop.
[!] The issue with passwordless decryption of DPAPI data has been
resolved by improving Windows Hello biometrics usage.
[!] A certain configuration of the GPU hybrid dictionary attack,
along with a vast set of rules, was causing the program to
stick for a couple of minutes after starting the attack. This
version has a fix for the problem.
[!] A fix for the error monitoring temperature/utilization/fan
on some machines with AMD devices.
[!] Some GUI issues in visual mask builder.
[!] There was a bug in DCC2 password recovery hash using a GPU.
On some hashes/users the program was unable to find a password.
[!] Super rules in a Hybrid dictionary attack were working
incorrectly.
