Portable Andriller – Android Forensic Tools 3.5.1
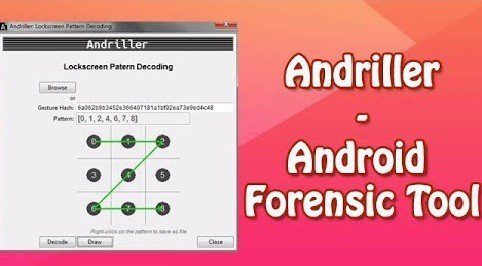
Andriller Portable is software utility with a collection of forensic tools for smartphones. It performs read-only, forensically sound, non-destructive acquisition from Android devices. It has features, such as powerful Lockscreen cracking for Pattern, PIN code, or Password; custom decoders for Apps data from Android (some Apple iOS & Windows) databases for decoding communications. Extraction and decoders produce reports in HTML and Excel formats.
Features:
- Automated data extraction and decoding
- Data extraction of non-rooted without devices by Android Backup (Android versions 4.x)
- Data extraction with root permissions: root ADB daemon, CWM recovery mode, or SU binary (Superuser/SuperSU)
- Data parsing and decoding for Folder structure, Tarball files (from nanddroid backups), and Android Backup (‘backup.ab’ files)
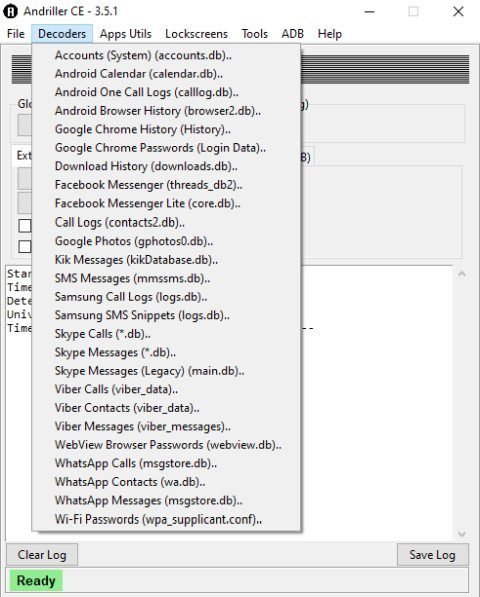
- Selection of individual database decoders for Android and Apple
- Decryption of encrypted WhatsApp archived databases (msgstore.db.crypt to *.crypt12)
- Lockscreen cracking for Pattern, PIN, Password
- Unpacking the Android backup files
- Screen captures of device display
Database Decoders
This feature allows importing individual App database files for automated parsing of the data. There are decoders mainly for Android and some for Apple iOS Apps. Once successfully decoded, reports will be shown your web browser. Databases can be exported from mainstream forensic tools, such as XRY, UFED Cellebite, Oxygen Forensic, and imported into Andriller for individual decoding. The output from Andriller offers cleaner output data.
Folder Structure
This will parse folder structures from Android filesystems and will produce Andriller style reports. These could be exports of filesystem from raw image files, or from ‘adb pull /data’ extractions, or unpacked ‘.tar’ files content.
Tarball Files
This will parse and decode nanddroid backup files such as ‘data.tar’ (including concatenated files), and will produce Andriller style reports. Nanddroid tarball backups are usually produced by custom recoveries, such as ClockWorkMod and TWRP.
Android Backup Files
This will parse and decode ‘backup.ab’ files, and will produce Andriller style reports.
What’s new:
- Critical fix in WhatsApp crypt decoding.
- Improved SQLite database handling on erroneous text entries.
- Bugfix in decoding databases containing additional sources, which affected decoders for: “Facebook”, “Kik”, “WhatsApp”.
- Bugfix date decoding in “Android Browser History”.
- Added Python 3.9 to the tox test suite.