Portable Passmark OSForensics Professional v8.0.1000 (x64)

OSForensics Portable is a new digital investigation tool which lets you extract forensic data or uncover hidden information from computers. OSForensics has a number of unique features which make the discovery of relevant forensic data even faster, such as high-performance deep file searching and indexing, e-mail and e-mail archive searching and the ability to analyze recent system activity and active memory. OSForensics can build and let you view an events timeline which shows you the context and time of activities. You can even recover data and files that have been deleted by users. OSForensics comes with a built-in file viewer which lets you examine a file contents, properties and meta-data, as well as an e-mail viewer which is compatible with most popular mail client formats.
Features:
Discover Forensic Evidence Faster
Find files faster, search by filename, size and time
Search within file contents using the Zoom search engine
Search through email archives from Outlook, ThunderBird, Mozilla and more
Recover and search deleted files
Uncover recent activity of website visits, downloads and logins
Collect detailed system information
Password recovery from web browsers, decryption of office documents
Discover and reveal hidden areas in your hard disk
Browse Volume Shadow copies to see past versions of files
Identify Suspicious Files and Activity
Verify and match files with MD5, SHA-1 and SHA-256 hashes
Find misnamed files where the contents don’t match their extension
Create and compare drive signatures to identify differences
Timeline viewer provides a visual representation of system activity over time
File viewer that can display streams, hex, text, images and meta data
Email viewer that can display messages directly from the archive
Registry viewer to allow easy access to Windows registry hive files
File system browser for explorer-like navigation of supported file systems on physical drives, volumes and images
Raw disk viewer to navigate and search through the raw disk bytes on physical drives, volumes and images
Web browser to browse and capture online content for offline evidence management
ThumbCache viewer to browse the Windows thumbnail cache database for evidence of images/files that may have once been in the system
SQLite database browser to view the and analyze the contents of SQLite database files
ESEDB viewer to view and analyze the contents of ESE DB (.edb) database files, a common storage format used by various Microsoft applications
Prefetch viewer to identify the time and frequency of applications that been running on the system, and thus recorded by the O/S’s Prefetcher
Plist viewer to view the contents of Plist files commonly used by MacOS, OSX, and iOS to store settings
$UsnJrnl viewer to view the entries stored in the USN Journal which is used by NTFS to track changes to the volume
Manage Your Digital Investigation
Case management enables you to aggregate and organize results and case items
HTML case reports provide a summary of all results and items you have associated with a case
Centralized management of storage devices for convenient access across all OSForensics’ functionality
Drive imaging for creating/restoring an exact copy of a storage device
Rebuild RAID arrays from individual disk images
Install OSForensics on a USB flash drive for more portability
Maintain a secure log of the exact activities carried out during the course of the investigation
Professional and Bootable Editions
The professional and bootable editions of OSForensics Portable have many features not available in the free edition, including:
Import and export of hash sets
Customizable system information gathering
No limits on the amount of cases being managed through OSForensics
Restoration of multiple deleted files in one operation
List and search for alternate file streams
Sort image files by colour
Disk indexing and searching not restricted to a fixed number of files
No watermark on web captures
Multi-core acceleration for file decryption
Customizable System Information Gathering
View NTFS directory $I30 entries to identify potential hidden/deleted files
New in OSForensics Portable v8
- Added New Face Detection module module for still photographs & images
- “Detect Faces” button was added in the Image Viewer
- “Sort by Faces” in File Name Search
- Added new Web Server Log Viewer module
- Can load up log files from Apache, IIS and other web servers, then filter and sort the log data
- Added new Python Scripting module
- Implemented new scripting engine, which allows access to internal OSF functions from Python scripting. Scripting commands such as osf.UserActivityGetResult(), osf.ReportGenerate() & osf.LogicalImageStart() are now available
- Changed ‘Run Python script’ to ‘OSF Script Player’
- Added support for built-in script templates installed under ProgramData\PassMark\OSForensics\ScriptTemplates. The template can be selected under the ‘New Script’ button dropdown
- Added Python API reference for help file.
- Added script examples for charting via matplotlib
- Add right-click menu to enter user-defined parameters to ‘pip install’
- Added new Cloud Imaging support for Forensic Imaging
- Added Cloud Download/Imaging for Google Drive, Microsoft OneDrive and Dropbox
- Cloud imaging will create empty files (0 byte files with “.deleted” extension) for deleted items from Dropbox. Dropbox includes deleted files in their directory listing
- Cloud Email Download support
- Added GMail export to MBOX format
- Added Microsoft Outlook (webmail) export to MBOX format
- AmCache Viewer
- Improved performance of reading amcache hive
- Auto Triage
- Turned off default options for including System hibernation and page files and registry files as part of the logical image configuration
- Started saving scan options and logical image options to config file
- Fixed display/gui bug where the background of the scan options was not being updated in WinPE
- Boot Virtual Machine
- Added the ability to select additional hard drives (data drives) when booting a VM from a disk image
- Case Management
- Added support for opening tagged e-mails & attachments via double-click/right-click
- Will now use Web Browser to open URL tags
- Added support for selecting multiple files when adding evidence images to case
- Add button to open ‘Manage Devices’ window, for managing the devices added to the case
- Multiple select enabled for Case Management. Can now delete or export multiple cases at a time
- Generate Report, updated to hide the categories that have no items
- Create / Search Index
- Added indexing for HEIC and HEIF image files
- Allowed indexing of memory dump files. .mem, Including .dmp, .mdmp (large file support does not apply if inside ZIP files)
- Improved speed of large binary file extraction indexing (by way of parallel / 2 thread concurrency)
- Fixed bytes progress status when indexing large binary file
- Added Email Attachment indexing options (“index attachments by file types”)
- Fixed exiftool indexing issue (using the -fast3 parameter culled out alot of necessary meta information AND may incorrectly identify file type. Note removed -fast optimization will now be slower)
- Fixed indexing of some GPS meta information from exiftool
- Fixed issue with indexing OCR output from HEIC and HEIF files
- Added “Save to Disk” for checked items
- Create/Compare Signature
- Combined the create and compare into a single “Signatures” module with separate tabs
- Added support for SHA-256 hashes. This required changing the signature file format and incrementing the signature file version from 6 -> 7
- Add support for comparing previous signature file version with v7 signature file
- Added options to have two hashing options (e.g. MD5 and SHA-256) for OSFSig and file listing. Note: Will work with V7 OSFSig files but not previous OSFV8 Beta OSFSig files before this commit. When comparing signatures with different hashing options, only signatures with matching hash will be compared. E.g. Sig1.OSFSig was created with MD5 only and Sig2.OSFSig was created with MD5 + SHA-256. Only MD5 will be used for comparison. If both signature files use the same hashing options both checksums will be used for comparison
- Deleted Files
- Enabled right-click menu option, Show File Location dialog, for deleted files on FAT filesystem. Note: The file location dialog will only show the first cluster of the deleted file for FAT filesystems as only the starting cluster is known and the link-list FAT entries for subsequent clusters are removed once a file is deleted on FAT filesystems
- Email Viewer
- Support opening single e-mails from PST/DBX/MBOX files for faster loading (check if this was also backported to V7)
- Added exporting e-mail messages to MSG file
- Add checkboxes to e-mail messages
- Added right-click option to export e-mails to PDF
- ESEDB Viewer:
- Fixed an issue where some values not displayed correctly in Windows 10 V2004
- File and Hex Viewer
- Added a drop down to allow track selection for playback for multi track video files
- Added “Analyze” button to Image Viewer to work with illicit image detection feature
- Fixed video player not working when opening video files via DirectAccess
- Fixed bug with video not playing when < 9 thumbnails were loaded
- Fixed a possible crash when extracting strings
- Video, Display duration of media along with current timestamp
- File Name Search
- Added “Illicit images” detection. File Name Search can now sort by “Illicit score”
- Changed configuration dialog to support modifying include/exclude folders for each preset. This allows for more accurate preset searches to be defined. Users can also define their own preset searches in the new advanced format
- Fixed bug in matching include/exclude folders in presets
- Fixed bug in saving custom preset include/exclude folders to XML file
- Preset searches now support included/excluded folders (currently, only by editing FileNameSearchPresets.cfg)
- Preset searches are now fixed and cannot be modified inline
- Added ‘User-defined Search’ for fully customizable search criteria
- Added right-click hash selected files option with option to create a Quick Hash Set from the results of the hashed files
- Added new preset for searching for large images + sort by face detection score
- Added new preset for searching for files modified since last month
- Added new preset for searching for files modified since yesterday
- Added colour backgrounds for results when sorting by Illicit or Face scores. Results are marked Red for likely illicit, Pink for probably illicit, and Green if Faces detected
- Minor UI layout updates
- Removed border from ‘Config’ text
- Increased width of preset/sorting combo box
- File System Browser
- File size units can be selected in the FSB options dialog. Defaults to “Auto” and will display in Human readable file size. File size units selectable are: Auto, Bytes, KB, MB, GB. Selection saved in OSFConfig file
- Fixed bug where the Analyze Shadow from the button within FSB was not working
- Consolidated filter text into single link control
- Changed timeline date type combo box to link control
- Removed ‘Current Path’ and added ‘Scan Status’ edit control
- Moved ‘Thumbnail size’ slider and ‘timeline date’ control to top
- Added ‘Images + Illicit-detect AI‘ preset
- Added “Video files (sorted by # Tracks)” preset
- Added sort by “video tracks” option
- Moved sorting combo box to the top
- Forensic Imaging
- Added option to select between single/split files when creating Encase E01 image files
- Added support for creating AFF4 disk images
- Enabled SMART logging in SysInfoLog.txt
- Hash Lookup
- Fixed crash when attempting to export lookup results to text
- Image Viewer
- Added support for HEIC and HEIF image files
- Added support for extracting meta data from HEIC and HEIF files
- Added Analyze Results popup window, showing results from AI face detect, AI illicit image detect, MD5, SHA1, etc
- Install PFX
- Fixed broken help file link
- Password Recovery
- Improved performance of reading Firefox, IE & Windows logins from registry
- Fix heap corruption when retrieving LSA secrets
- Fixed various memory leak issues
- Updated to support new Edge Chromium-based version.
- Updated to support Chrome V80 and beyond
- Updated to support Opera V67 and beyond
- Fixed the Password Length column to display Not Available message when the password is not decrypted
- Decryption Tab, Added ability for users to select multiple files at a time
- Removed support for Opera Version 22 and earlier
- Removed support for FireFox Version 31 and earlier
- Removed support for Safari
- Fixed potential crash when running on Windows 10 V2004.
- Made some changes to enable recovery of chrome, edge and opera passwords in some cases where it was previously failing
- Registry reading
- Improved performance of RegistryGetSubKeys() and RegistryGetKeyValues() methods for reading registry keys
- Improved performance of reading registry entries in User Activity. On a 160MB SOFTWARE hive, load times improved from >10min to 20s (as compared to v7.1.1005)
- Added new registry function to read a single key in a hive for better performance without loading the entire registry file
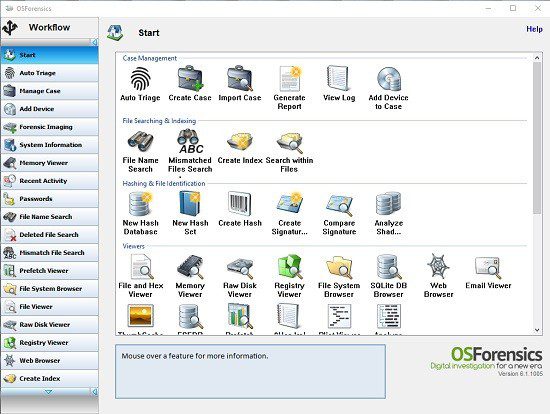
- Start
- Add new ‘Manage Devices’ icon
- System Information
- Will now pick “System information from registry” as default when live acquisition is not selected for the case
- Will now skip commands that can’t be run on the selected drive (eg live acquisition only and a drive letter is selected) and display a skipped message in the output
- Made some changes to allow user entered commands (eg regripper) to be run when live acquisition OR drive letter is selected (as most user entered commands will likely have a hard coded location)
- ThumbCache Viewer
- Redesigned the interface allowing to load a single cache file, add multiple files by scanning drive or folder
- Added a tree view to show list of added cache files, folders and drives
- Added a new “All” option to the Thumbnail Size combo box to show all records in a cache index file
- Added a new feature to allow loading multiple cache files and viewing all of the records in them in a single list view
- Added Extended Information to show EXIF data of thumbnails retrieved from ESE Database
- Updated the thumbnail preview window to be resizable
- Improved the efficiency of loading ESE Database
- Thumbnail View
- Added support for displaying thumbnails for video files
- Support for animated video thumbnails on mouse hover
- Changes to thumbnail caching thread for better performance and robustness
- Added support for deleted video thumbnails
- Files that do not have thumbnails are cached and no longer reloaded
- User Activity
- Added support for decrypting cookies value of the Chrome, Edge and Opera browsers
- Added support for decrypting form history value of the Edge browser
- Added Search Term to extract search keywords used in browsers
- Added Website Logins to obtain browser passwords
- Rearranged config dialog slightly to shrink height (previously unable to see OK button on 1080p laptop screen)
- P2P, added extra error information display for decoder error during P2P scan
- Fixed null pointer crash when scanning for USB devices only
- Fixed bug in opening ARES registry key path
- Added more Windows Event IDs to extract more forensically interesting logs
- Added times to Browser Bookmarks and WLAN items
- Fixed Time Source display error for some items under All category
- Changed list-view default sorting as date and time descending order
- Improved column sorting speed
- Updated column names for Autorun Commands and UserAssist
- Fixed an issue with Windows Search scan on Windows 10 V2004
- Updated Browser History, Downloads, Form, Bookmarks and Cookies to support the latest versions of Edge, Chrome and Opera browsers
- Updated Downloads to support Firefox latest versions
- Fixed and issue with Windows Search showing incorrect times in Windows 10 V2004
- Moved Top Sites items to Browser History category
- Removed support for Opera Version 22 and earlier
- Removed support for FireFox Version 31 and earlier
- Removed support for Safari
- Web Browser
- Fixed video download crash
- Workflow
- Workflow buttons and Start window icons now have 1-to-1 correspondence
- Removed extra ‘button’ slot
- Revised default workflow list
- Added separate checkbox column to show/hide icon in Start page, hiding workflow buttons no longer hide the corresponding Start page icon
- Misc
- Updated Volatility Workbench to v3.0.1001
- Updated exiftool to version 12.03
- Updated WinPEBuilder
- On exit, OSF will check the parent Temp folder to clean up orphaned temp directories. It will only delete the temp directories that are older than the oldest running/active osf32.exe or osf64.exe process
- Fixed a crash that could occur in the trial version in deleted files and file name search